Cyber threats are a perpetual reality for business owners. Hackers are constantly innovating. They devise new ways to exploit vulnerabilities in computer systems and networks. For businesses of all sizes, a proactive approach to cybersecurity is essential. One of the most crucial elements of this approach is regular vulnerability assessments. A vulnerability assessment is a… Continue reading Don’t Risk It! Why You Shouldn’t Skip Vulnerability Assessments
Category: Cybersecurity
7 Common Pitfalls When Adopting Zero Trust Security
Zero Trust security is rapidly transforming the cybersecurity landscape. It moves away from traditional perimeter-based security models. In this approach, every connection attempt is continuously verified before granting resource access. 56% of global organizations say adopting Zero Trust is a “Top” or “High” priority. This approach offers significant security advantages. But the transition process presents… Continue reading 7 Common Pitfalls When Adopting Zero Trust Security
Critical Security Tips for Remote and Hybrid Workers
The rise of remote and hybrid work models has transformed the way we work. Gone are the days of rigid office schedules and commutes. But with this flexibility comes a new set of challenges – cybersecurity threats. 20% of managers said their company experienced a security breach due to a remote worker. Here’s the truth:… Continue reading Critical Security Tips for Remote and Hybrid Workers
Guarding the Gates: How Continuous Monitoring Bolsters Cybersecurity
Organizations face a relentless barrage of cyberattacks in the digital age. From sophisticated malware to targeted phishing campaigns, the adversaries are persistent and adaptive. It’s projected that in 2031 the costs from ransomware will be over 10 times higher than they were in 2021. Last year, the average cost of a ransomware attack for a… Continue reading Guarding the Gates: How Continuous Monitoring Bolsters Cybersecurity
Here Are 5 Data Security Trends to Prepare for in 2024
With cyber threats evolving at an alarming pace, staying ahead of the curve is crucial. It’s a must for safeguarding sensitive information. Data security threats are becoming more sophisticated and prevalent. The landscape must change to keep up. In 2024, we can expect exciting developments alongside persistent challenges. Over 70% of business professionals say their… Continue reading Here Are 5 Data Security Trends to Prepare for in 2024
Google & Yahoo’s New DMARC Policy Shows Why Businesses Need Email Authentication… Now
Have you been hearing more about email authentication lately? There is a reason for that. It’s the prevalence of phishing as a major security threat. Phishing continues as the main cause of data breaches and security incidents. This has been the case for many years. A major shift in the email landscape is happening. The… Continue reading Google & Yahoo’s New DMARC Policy Shows Why Businesses Need Email Authentication… Now
Beware of Deepfakes! Learn How to Spot the Different Types
Have you ever seen a video of your favorite celebrity saying something outrageous? Then later, you find out it was completely fabricated? Or perhaps you’ve received an urgent email seemingly from your boss. But something felt off. Welcome to the world of deepfakes. This is a rapidly evolving technology that uses artificial intelligence (AI). It… Continue reading Beware of Deepfakes! Learn How to Spot the Different Types
AI Security Breaches Are on the Rise. What You Need to Know
Artificial intelligence (AI) is rapidly transforming our world. From ChatGPT to Copilot in Microsoft 365, AI is revolutionizing how we do business. But with great power comes great responsibility, and AI is no exception. A recent study revealed a worrying trend: AI security breaches are on the rise. The study by HiddenLayer titled AI Threat… Continue reading AI Security Breaches Are on the Rise. What You Need to Know
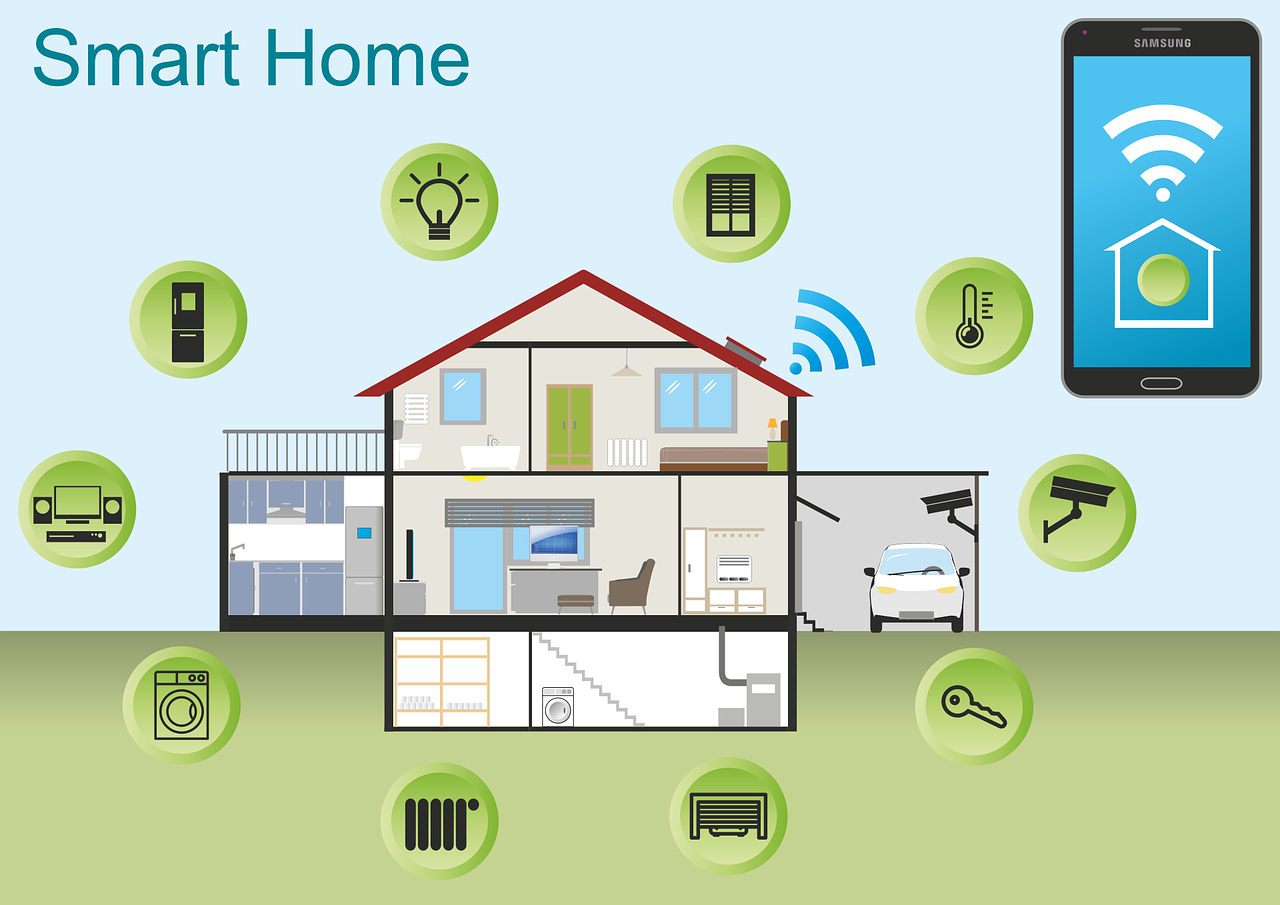
10 Most Common Smart Home Issues (and How to Fix Them)
Back when you were a kid, living in a “smart home” probably sounded futuristic. Something out of Back to the Future II or The Jetsons. Well, we don’t yet have flying cars, but we do have video telephones as well as smart refrigerators and voice-activated lights. But even the most advanced technology can have analog… Continue reading 10 Most Common Smart Home Issues (and How to Fix Them)
Comprehensive Guide for Fostering a Cyber-Aware Culture
In today’s interconnected digital landscape, cybersecurity has become an indispensable aspect of any organization’s operations. With cyber threats evolving in complexity and frequency, fostering a culture of cyber awareness within an organization is paramount to mitigate risks effectively. A cyber-aware culture encompasses not only the implementation of robust technical measures but also the cultivation of… Continue reading Comprehensive Guide for Fostering a Cyber-Aware Culture